Did you know? Employees you perceive as reliable and trustworthy might actually pose a potential cybersecurity threat.
Recent studies indicate that nearly 60% of data breaches stem from insider threats. Insiders can either carry out attacks themselves or unintentionally become targets for external attackers. As we enter 2024, the need to protect against insider threats has never been more pressing. In this changing scenario, creative approaches are crucial to safeguard organizational assets. Join us as we explore five compelling measures to fortify defenses against insider threats.
- Behavioral Monitoring and Analytics: Employ AI-powered systems to monitor and analyze user activities, communication patterns, and data access for unusual behavior that might indicate a security threat.
For instance, anomalies like
- changes in user behavior,
- unexpected data downloads, or
- attempts to access unauthorized systems or files
should be carefully scrutinized to identify and prevent threats.
- Data Loss Prevention (DLP) and Endpoint Security: Advanced Data Loss Prevention (DLP) solutions help detect and prevent the unauthorized exfiltration of sensitive data. Endpoint security tools can monitor devices for suspicious file modifications, unauthorized applications, and attempts to bypass security measures.
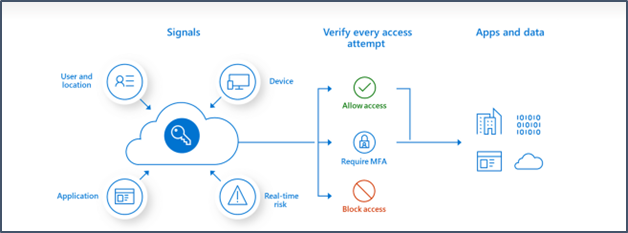
- Identity and Access Management (IAM) with Zero Trust: Establish a robust Identity and Access Management (IAM) system with a zero trust approach. This includes granting least privilege access, implementing multi-factor authentication for added security, and enforcing continuous authorization controls to monitor and mitigate potential insider threats effectively.
- User Education and Awareness Programs: Conduct routine training programs for employees and stakeholders to educate them about insider threats. Instruct them on identifying suspicious activity and emphasize the significance of reporting potential security breaches promptly. Nurture a culture of cybersecurity awareness to enhance preventive measures.
5 Tips to Encourage Employees to Adopt Best Cybersecurity Practices.
- Relate security to personal life with real-world examples.
- Engage with interactive training, gamification, and rewards.
- Lead by example with consistent good security practices.
- Prioritize convenience with user-friendly tools and streamlined procedures.
- Celebrate successes for a strong security culture.
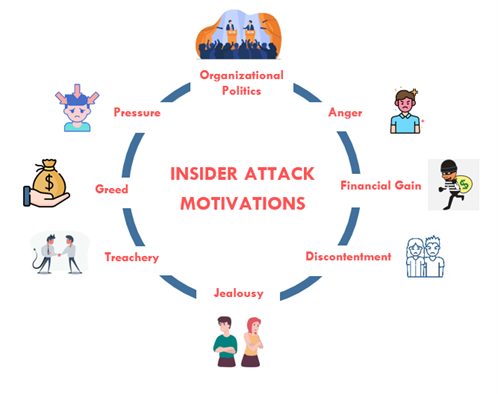
- Psychological and Social Factors: Identify potential motivations behind insider threats, such as disgruntlement, financial pressure, or ideological extremism. This can help your organization implement targeted preventive measures and address underlying issues.
Emerging Strategies:
Continuous Authentication: Monitoring user behavior and adapting security measures in real-time can further mitigate the risk of unauthorized access or data exfiltration.
Deception Technology: Deploying decoy data and systems can lure potential insiders and gather valuable intelligence on their actions and motivations.
Artificial Intelligence and Machine Learning: Leveraging AI to analyze vast amounts of data and identify subtle patterns can predict and prevent insider threats with greater accuracy.
Remember:
- Preventative measures are key: Early detection and intervention are crucial to minimize the impact of an insider threat.
- Balance security with privacy: Striking a balance between robust security measures and employee privacy is essential.
- Foster a culture of security: Open communication, trust, and employee engagement are vital in preventing insider threats.
Conclusion:
In the world of cybersecurity, dealing with insider threats requires both technology and a deep understanding of human behavior. Here, success isn’t just about using security tools; it’s about shaping a mindset. Prevention is crucial, and having a culture focused on security is the foundation of resilience.
By adopting advanced measures and fostering a culture of security, you not only face insider challenges but triumph over them, Your data and assets aren’t just protected; they’re fortified against the ever-changing digital landscape.



