Understanding DDoS Attacks and Mitigation Techniques
The year is 2016, and as the clock strikes 11:10 UTC on October 21st, a storm of relentless cyberattacks shakes the foundations of the internet. The Dyn DDoS attack is being orchestrated by the notorious Mirai botnet, an army of infected Internet of Things (IoT) devices.
As the attack intensifies, major websites and services like Twitter, Netflix, The New York Times, GitHub crumble and become inaccessible to users.
In the digital landscape, Distributed Denial of Service (DDoS) attacks pose a significant threat to businesses of all sizes. Understanding DDoS attacks and implementing effective mitigation techniques is crucial for companies to protect their online presence and maintain business continuity.
What is a DDoS Attack?
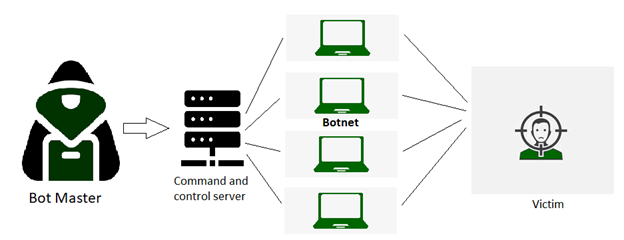
Imagine a website or online service being flooded with an overwhelming number of requests all at once. This flood of traffic comes from multiple sources, making it difficult to identify the attackers and block them. DDoS attacks use a network of compromised devices, often called “botnets,” to launch this massive flood of traffic simultaneously, causing the target’s servers to become overloaded and unresponsive.
The Impact of DDoS Attacks on Businesses
DDoS attacks can severely impact businesses on many levels. They can lead to website downtime, which means customers cannot access the company’s services, causing frustration and loss of revenue. Moreover, DDoS attacks can also serve as a distraction tactic, diverting attention from other cyber threats and potentially leading to serious security breaches.
Mitigation Strategies for DDoS Attacks
To safeguard against DDoS attacks, companies can adopt various mitigation strategies to detect and mitigate these attacks promptly. Here are some of the best techniques:
Content Delivery Network (CDN): A CDN can distribute website content across multiple servers in different regions. This reduces the impact of DDoS attacks by distributing the traffic and making it easier to filter out malicious requests.
Traffic Filtering: Employing traffic filtering solutions allows companies to inspect incoming traffic and identify and block suspicious or malicious requests. This technique helps isolate and mitigate DDoS attacks before they reach the company’s servers.
Rate Limiting: Setting up rate limiting rules helps control the number of requests allowed from a single IP address within a specific timeframe. By limiting the number of requests from each source, DDoS attackers are restricted in their ability to overwhelm the target.
Cloud-Based DDoS Protection: Cloud-based DDoS protection services use vast network infrastructures to absorb and mitigate DDoS traffic before it reaches the company’s servers.
Load Balancing: Load balancing distributes incoming traffic across multiple servers to ensure no single server is overloaded. This technique can help maintain service availability during DDoS attacks.
Role of IAM in DDoS Attack Detection and Response
Identity and Access Management (IAM) aids in early detection and response to DDoS attacks. Here’s how IAM can help:
User Behavior Analytics: IAM solutions monitor and analyze user behavior patterns. Unusual spikes in login attempts or abnormal access patterns may indicate a potential DDoS attack.
Multi-Factor Authentication (MFA): MFA adds extra security by asking users for more than one verification when they log in. This stops unauthorized access and DDoS attacks from hacked accounts.
Centralized Access Control: IAM helps organizations manage user access in one central place. It ensures that only authorized users can access sensitive resources, reducing the chances of DDoS attacks.
Real-Time Monitoring: IAM solutions can monitor what users do in real-time. If they spot anything suspicious, like strange access requests, they can quickly respond by blocking access temporarily. This prevents DDoS attacks from causing too much damage.
Choose MetroMax for Industry-Best IAM Solutions!
DDoS attacks continue to be a significant concern for businesses, but with proper mitigation strategies and robust IAM solutions, you can strengthen the defenses against cyberattacks.


